Whereas DNS focuses on simplification by using workstation names instead of addresses, the Network Information Service (NIS) focuses on simplifying network administration by providing centralized control over a variety of network information. NIS stores information not only about workstation names and addresses, but also about users, the network itself, and network services. This collection of network information is referred to as the NIS namespace.
NIS uses a client-server arrangement similar to DNS. Replicated NIS servers provide services to NIS clients. The principal servers are called master servers and, for reliability, they have backup or replica servers (also referred to as slave servers). Both server types use the NIS information retrieval software and both store NIS maps. The method used by NIS+ is described briefly in the Network Information Service+ (NIS+) Overview.
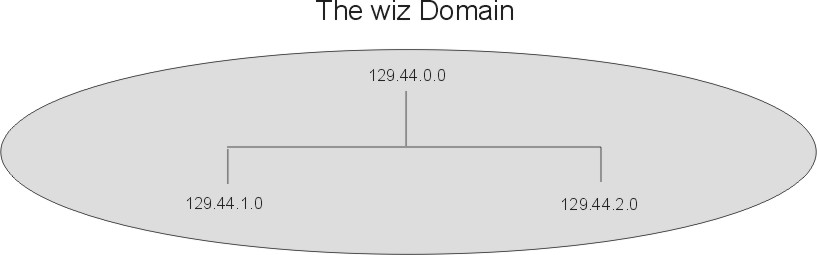
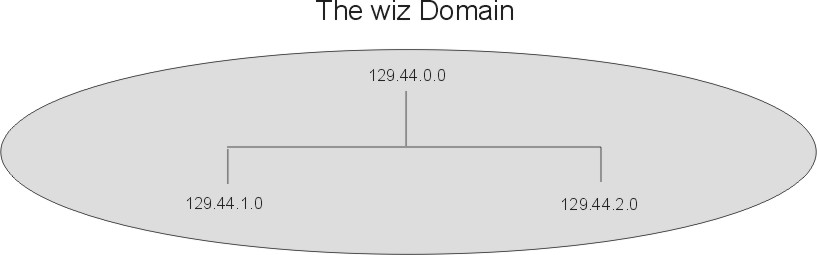
NIS, like DNS, uses domains to arrange the workstations, users, and networks in its namespace. However, it does not use a domain hierarchy; an NIS namespace is flat. Thus, a hierarchical physical network is arranged by NIS into one domain, as shown in the following figure. See Chapter 4, NIS+ Namespace and Structure for information on NIS+ hierarchy.
Figure 1-4. Example NIS Domain. An example domain, named wiz, with one server IP address and two subordinate workstation IP addresses.
 |
An NIS domain cannot be connected directly to the Internet. Organizations that want to use NIS and be connected to the Internet use NIS to manage all local information and DNS for host name resolution. NIS provides special client routines for this purpose (DNS forwarding). When a client needs access to any type of information except IP addresses, the request goes to the client's NIS server. When a client needs name resolution, the request goes to the DNS server. From the DNS server, the client has access to the Internet in the usual way.
NIS stores information in a set of files called maps. NIS maps were designed to replace traditional UNIX /etc files, as well as other configuration files, so they store much more than names and addresses. As a result, the NIS namespace has a large set of maps, as shown in the NIS Maps table below.
NIS maps are essentially two-column tables. One column is the key
and the other column is information about the key. NIS finds
information for a client by searching through the keys. Thus, some
information is stored in several maps because each map uses a different
key. For example, the names and addresses of workstations are stored in
two maps: hosts.byname and
hosts.byaddr. When a server has a workstation's
name and needs to find its address, it looks in the
hosts.byname map. When it has the address and needs
to find the name, it looks in the hosts.byaddr map.
| NIS Maps | |
|---|---|
| NIS Map | Description |
| bootparams | Lists the names of the diskless clients and the location of the files they need during booting. |
| ethers.byaddr | Lists the Ethernet addresses of workstations and their corresponding names. |
| ethers.byname | Lists the names of workstations and their corresponding Ethernet addresses. |
| group.bygid | Provides membership information about groups, using the group ID as the key. |
| group.byname | Provides membership information about groups, using the group name as the key. |
| hosts.byaddr | Lists the names and addresses of workstations, using the address as the key. |
| hosts.byname | Lists the names and addresses of workstations, using the name as the key. |
| mail.aliases | Lists the mail aliases in the namespace and all the workstations that belong to them. |
| mail.byaddr | Lists the mail aliases in the namespace, using the address as the key. |
| netgroup | Contains netgroup information, using the group name as the key. |
| netgroup.byhost | Contains information about the netgroups in the namespace, using workstation names as the key. |
| netgroup.byuser | Contains netgroup information, using the user as the key. |
| netid.byname | Contains the Secure remote procedure call (RPC) netname of workstations and users, along with their user IDs and group IDs. |
| netmasks.byaddr | Contains network masks used with Internet Protocol (IP) subnetting, using the address as the key. |
| networks.byaddr | Contains the names and addresses of the networks in the namespace, and their Internet addresses. |
| networks.byname | Contains the names and addresses of the networks in the namespace, using the names as the key. |
| passwd.byname | Contains password information, with the username as the key. |
| passwd.byuid | Contains password information, with the user ID as the key. |
| protocols.byname | Lists the network protocols used. |
| protocols.bynumber | Lists the network protocols used but uses their number as the key. |
| publickey.byname | Contains public and secret keys for Secure RPC. |
| rpc.bynumber | Lists the known program name and number of RPCs. |
| services.byname | Lists the available Internet services. |
| ypservers | Lists the NIS servers in the namespace, along with their IP addresses. |
Chapter 2, Network Information Service contains detail about the development and use of NIS.